This week we discovered a hospital in Illinois using ExecProtect to enforce corporate communication policies within their organization. This post is about why they initially chose ExecProtect and how they used it to gain additional value.
What is ExecProtect?
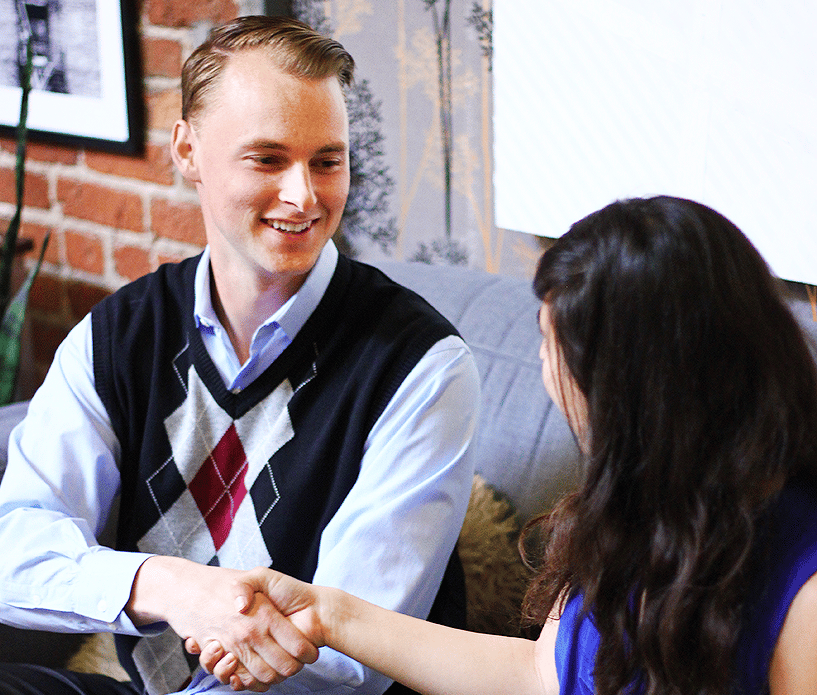
 Screenshot of a Display Name Spoofing attack stopped by ExecProtect
Screenshot of a Display Name Spoofing attack stopped by ExecProtect
ExecProtect, which is a concatenated version of Executive Protection, is a new feature we added to Paubox Email Suite Plus.
We built ExecProtect to combat advanced Display Name Spoofing attacks that are crippling organizations across the internet.
As a recap, Display Name Spoofing attacks appear to come from a person of authority (i.e. executive) within a company.
When this is coupled with:
- The fact that at least 70% of all email is now read from a smartphone.
- By default, email apps on a smartphone only show the Display Name of the sender. If you want to see the actual email address, further action (i.e. friction) is required.
The net effect is that if you see an email from your boss on your phone, you’ll probably open it immediately, not bothering to think about the actual email address it came from.
In other words, executives are being impersonated by bad actors to perpetrate fraud against their organizations.
Why Choose ExecProtect?
Customers are choosing ExecProtect because it stops Display Name Spoofing attacks dead cold.
Instead of appending disclaimers like:
- [External]
- "This email is from outside our organization"
to the body or subject line of a Display Name Spoof attack, we designed ExecProtect to immediately quarantine the message and send an alert of the IT administrator.
This approach achieves two objectives:
- It prevents the Display Name Spoof attack from reaching the end user's inbox.
- It quickly demonstrates value to the IT administrator
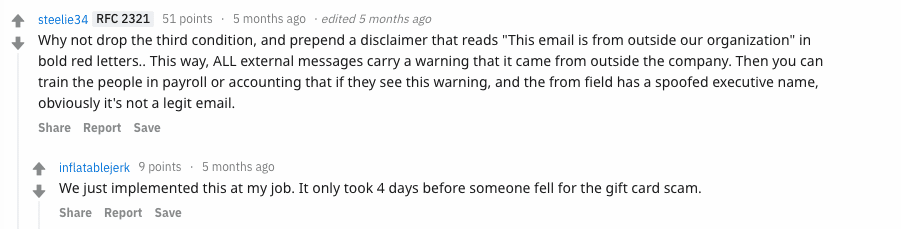
In addition, we can see from this recent Reddit thread that appending disclaimers to these phishing attacks simply does not work.
The correct approach is stopping the phishing attack from ever reaching the user's inbox.
Enforcing Email Policies with ExecProtect
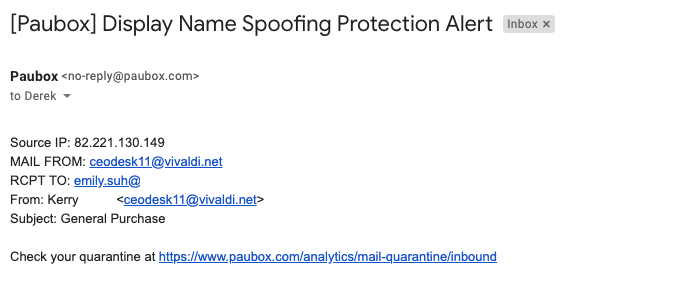
During a check-in with our customer in Illinois this week, we learned they are using ExecProtect to also enforce corporate email policy.
Here's the email policy the hospital wanted to enforce:
- Personal email addresses are not allowed for business purposes
After enabling ExecProtect, valid email sent from executives' personal accounts like Gmail and AOL got immediately quarantined.
In other words, ExecProtect helped them achieve their organizational email policies.
Conclusion: ExecProtect Can Provide Double Value
In addition to Display Name Spoofing protection, our customer was able to leverage ExecProtect to achieve the secret bonus of policy enforcement for their organization's email.
Subscribe to Paubox Weekly
Every Friday we bring you the most important news from Paubox. Our aim is to make you smarter, faster.

 Hoala Greevy
Hoala Greevy