1 min read

We wrote earlier this year about ransomware making the rounds among U.S. hospitals. Especially worrying is the fact that some of these hospitals actually paid the ransom! As you'd expect, this just encourages the behavior.
SEE RELATED: PowerWare Ransomware is Healthcare’s New Security Threat
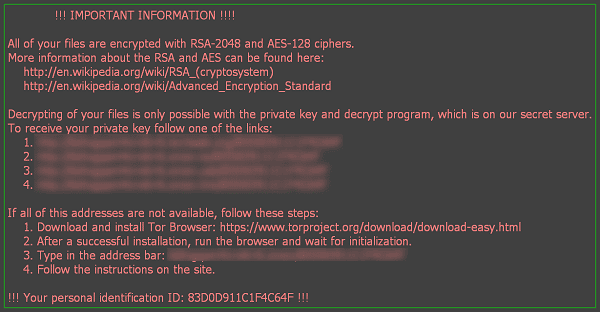
The latest ransomware attacking U.S. Healthcare is known as Locky. It gets its name because it renames crucial files to have the extension .locky. In addition, it also encrypts the files using a secret encryption key that can only be purchased via bitcoin. In other words, pay a ransom to get your files decrypted.
The primary method of infection has been through spam and phishing email campaigns, many of which are disguised as invoices or resumes. Word or Excel documents containing a malicious macro are attached to these emails.
Recent variants of Locky are now using DOCM files (macro-enabled files used in Microsoft Word) to deliver the ransomware.
Paubox Clamps Down on Deadly Macros and Ransomware
At Paubox, we've taken a forward-looking approach to ransomware. We believe the future of email does not include the practice of sending email attachments containing macros. In fact, we’ve reached the conclusion that the business downsides affiliated with attachments containing macros now outweigh its business benefits. Similar to how people got used to not sending EXE files via email in the early 2000s, we believe the same is now true for sending macros via email. Paubox automatically places any incoming email containing a macro in the Paubox Quarantine. As far as I know, we are the first company to take this proactive stance against Locky ransomware and whatever else will come along after it.
SEE ALSO: We’re Clamping Down on Deadly Macros and Ransomware
Subscribe to Paubox Weekly
Every Friday we bring you the most important news from Paubox. Our aim is to make you smarter, faster.

 Hoala Greevy
Hoala Greevy