We all know that a phishing email can hurt its recipients because they can unknowingly download malware or share confidential information under false pretenses.
One of the tactics used in phishing attacks is display name spoofing, where the "from" email address looks like it's coming from a legitimate domain, but is actually from a fraudulent sender. This can cause real problems for many companies, where real emails get mixed up with the fake ones, resulting in many legitimate emails ending up undelivered, deleted, or stuck in the spam folder.
That’s exactly why organizations should incorporate email authentication methods such as DKIM, SPF, and DMARC in their email security strategy. We already discussed DKIM and DMARC, so let’s move to SPF.
What is SPF and how does it work?
Sender Policy Framework (SPF) is a method that lets a domain owner identify the servers they have approved to send emails on behalf of their domain. A message with a forged sender will not pass the SPF check, because the server it comes from hasn’t been approved by the entity it pretends to be.
For example, a phishing email pretending to be your bank may display a "from" email address like support@yourbank.com, but actually be sent from a separate server.
In short, SPF checks makes sure that an incoming email was really sent by the server it says it was sent from.
The inner workings of SPF
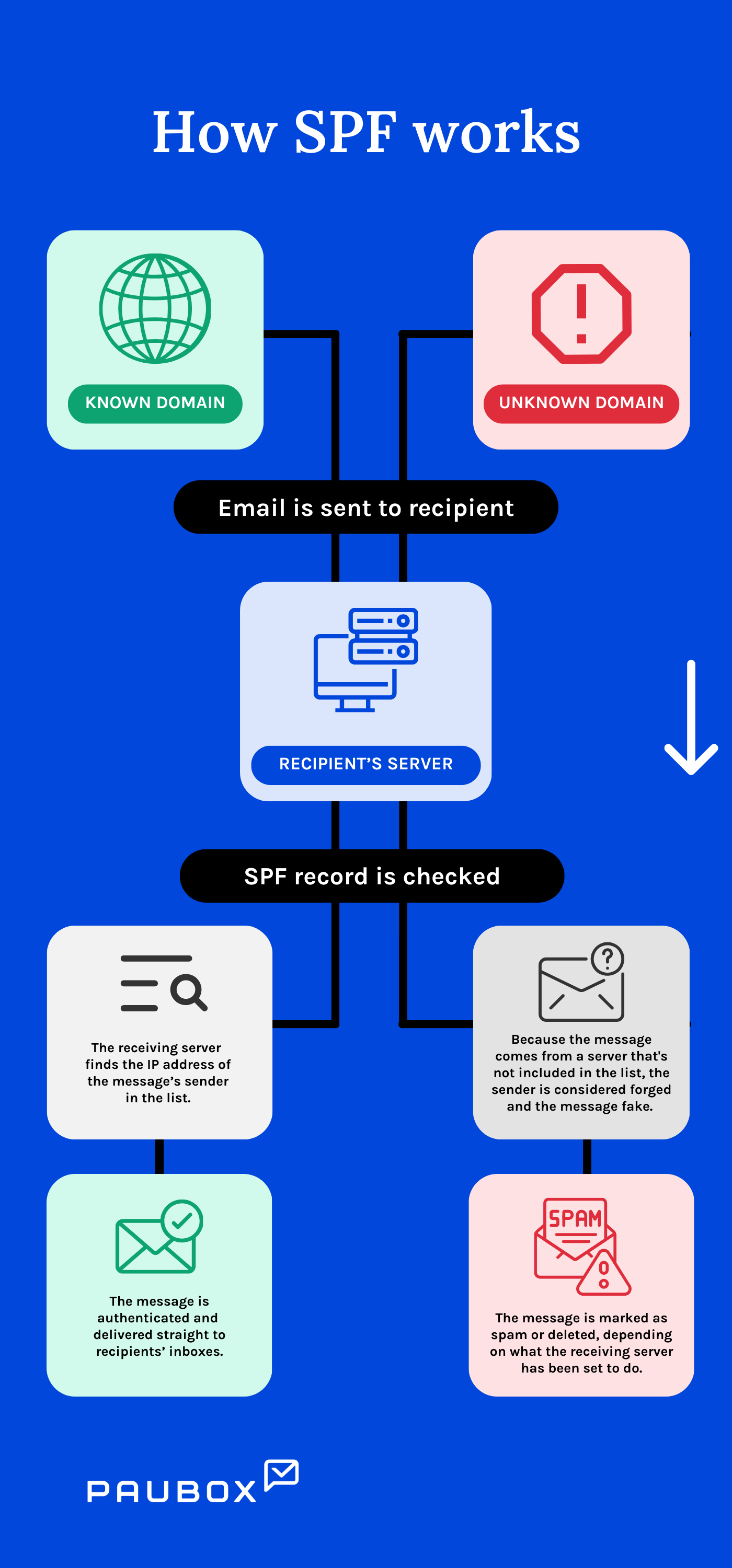
To setup an SPF record for your company, you first list the IP addresses of the servers you have authorized to send emails for your organization.
Then, you publish the SPF records in your DNS as TXT entries. Let’s say a spammer spoofs your organization’s email address and sends a phishing email to stakeholders.
During an SPF check, the receiving server compares the IP address of the message’s sender to the list of IP addresses you published in the DNS. Because the message comes from a server that's not included in the list, the sender is considered forged and the message fake. It is then marked as spam or deleted entirely, depending on what the receiving server has been set to do when encountering fraudulent emails. But if your organization sends a real email to stakeholders, the receiving server will find the IP address of the message’s sender in the list. The message is authenticated and delivered straight to recipients’ inboxes where it rightfully belongs.
Your organization likely owns several domains, and only some of them are used to send emails. But it's still advisable to create SPF records for all your organization's domains so that spammers can't successfully spoof any one of them.
How Paubox helps
Like DKIM, SPF is an effective means of email authentication which Paubox Email Suite Plus can provide for you.
One of the hundreds of checks Paubox Email Suite Plus makes against incoming emails includes validating DKIM, SPF and DMARC records.
But SPF isn’t perfect. Once a message is forwarded, the SPF check breaks. Also, SPF checks work well only if SPF records are always updated, but that’s not always the case. What your inbox needs is additional protection such as the advanced threat detection features Paubox Email Suite Plus offers, like ExecProtect which stops display name spoofing attacks from reaching users in the first place.
Subscribe to Paubox Weekly
Every Friday we bring you the most important news from Paubox. Our aim is to make you smarter, faster.