Small and medium healthcare organizations have a new version of the Security Risk Assessment (SRA) tool . The SRA tool is a collaborative effort between The Office of the National Coordinator for Health Information Technology (ONC) and the HHS Office for Civil Rights (OCR). It was developed for healthcare providers to assess security risks to their protected health information ( PHI ).
Small and medium healthcare organizations have a new version of the Security Risk Assessment (SRA) tool . The SRA tool is a collaborative effort between The Office of the National Coordinator for Health Information Technology (ONC) and the HHS Office for Civil Rights (OCR). It was developed for healthcare providers to assess security risks to their protected health information ( PHI ).
What does the SRA tool accomplish?
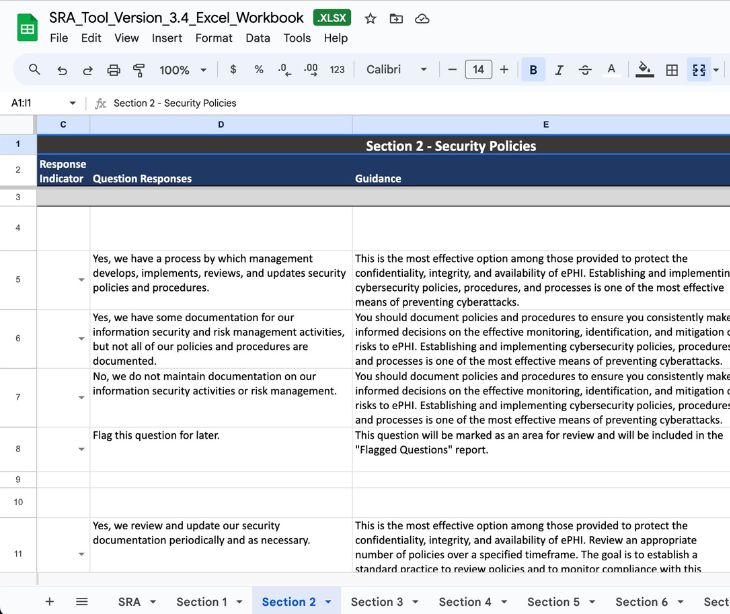
The updated version of the HHS Security Risk Assessment tool is more user-friendly and can determine the confidentiality, integrity, and availability risks of health information. Based on user feedback and public input, the SRA tool has several feature enhancements, including:- Improved navigation of assessment sections
- Modular workflow
- Custom assessment logic
- Progress tracker
- Enhanced user interface scaling
- Overall improvement of user experience
- Threats & vulnerabilities rating
- Detailed reports
- Options to export reports
- Business associate and asset tracking
How safe is the SRA tool?
The SRA tool collects information and stores it locally on the user’s tablet or computer. HHS does not access, collect, view, store, or transmit any of the information the SRA tool obtains. The user receives the assessment results in a report. It covers risks in policies, processes, and systems. The report also recommends methods to reduce weaknesses in security.Why should healthcare organizations use it?
HIPAA Security Rule requires healthcare organizations to conduct security risk assessments. The SRA tool helps healthcare providers ensure compliance with HIPAA regulations concerning administrative, physical, and technical safeguards to protect PHI. You should note that the SRA tool is for informational purposes only. Even though it may reflect the current best practices of information technology, it is not required to stay compliant with HIPAA’s Security Rule requirements. Healthcare providers should always consult with experts about their security system.How does encryption fit in?
Encryption requirements around PHI are “addressable” in the HIPAA Security Rule, which means that encryption is not necessarily required to manage risks to PHI transmission. But it can be an excellent option to protect your healthcare data. When it comes to sending HIPAA compliant email , HHS suggests that covered entities use encryption for electronic PHI (ePHI) transmission “whenever deemed appropriate.” A healthcare organization could opt not to encrypt emails, but it would need to document its decision-making process and implement an alternative solution to safeguard ePHI. However, there’s not much of an alternative option to email encryption, and you can never be too safe with guarding valuable healthcare information. Paubox Email Suite offers encryption by default. After implementing the solution, every email you send will be encrypted. This is the maximum protection you can get for safeguarding your emails and PHI.Subscribe to Paubox Weekly
Every Friday we'll bring you the most important news from Paubox. Our aim is to make you smarter, faster.