1 min read
Monitoring encryption and data security measures for HIPAA compliance
Liyanda Tembani
October 5, 2023

HIPAA compliance involves scrutiny of security tools, ongoing audits, and an examination of security policies and procedures. The objective is to ensure that PHI remains confidential, secure, and accessible only to authorized personnel.
Monitoring encryption and data security measures entails regularly assessing the effectiveness of systems and practices to safeguard sensitive healthcare data.
Understanding HIPAA requirements
HIPAA regulations outline specific requirements for the security of PHI. The HIPAA Security Rule, in particular, emphasizes encryption and other security measures to safeguard patient data. The consequences of non-compliance are severe, potentially resulting in substantial fines and damage to an organization's reputation. As a result, healthcare organizations must remain proactive and vigilant in meeting these requirements.
What are encryption and data security mechanisms?
Encryption involves transforming data into a secure, unreadable format that can only be deciphered with the appropriate encryption keys.
Alongside encryption are various data security mechanisms:
- Access controls
- Authentication
- Authorization
These layers of protection ensure that only authorized individuals can access and manipulate patient information.
Related: Encryption at rest: what you need to know
The elements of monitoring for HIPAA compliance
- Continuous monitoring: Healthcare organizations must identify the critical components that require monitoring, which typically encompass Electronic Health Records (EHRs), databases, communication channels, and even physical access to data centers or server rooms.
- Tools and technologies for monitoring: Effectively monitoring encryption and data security necessitates specialized tools and technologies. Security Information and Event Management (SIEM) systems, intrusion detection/prevention systems, and other advanced solutions play a role in real-time threat detection. These tools provide insights into potential threats and vulnerabilities, enabling healthcare organizations to take proactive measures.
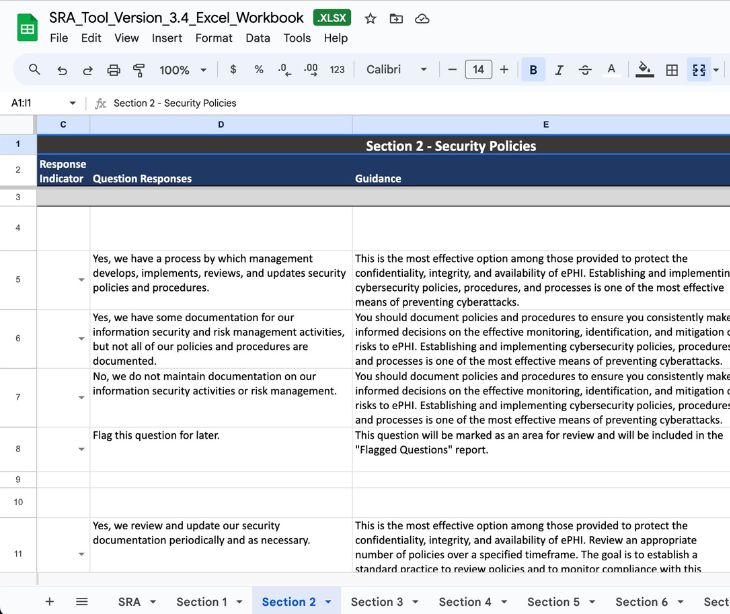
- Establishing effective policies and procedures: Developing comprehensive and tailored monitoring policies and procedures helps ensure ongoing HIPAA compliance. These policies should define roles and responsibilities within the monitoring process, ensuring the entire organization is aligned with compliance objectives. Additionally, they should be subject to regular review and updates to keep pace with evolving threats and changing regulations.
- Continuous auditing and reporting: Healthcare organizations should implement robust strategies for conducting routine audits and reviews. Robust reporting mechanisms are equally important, serving as the foundation for documenting monitoring results and compliance status. These reports not only help demonstrate compliance with regulatory bodies but also offer insights into potential areas for improvement.
Incident response and corrective actions
Monitoring serves a dual purpose—it detects security incidents and facilitates swift responses when incidents occur. Healthcare organizations must have a well-defined incident response plan. This plan should outline the steps to be taken in the event of a security incident or breach, including reporting to appropriate authorities and affected individuals.
Subscribe to Paubox Weekly
Every Friday we bring you the most important news from Paubox. Our aim is to make you smarter, faster.