1 min read
I recently had dinner in Honolulu with Preston Terada, IT Manager for Kahala Nui. During our dinner, I learned about Tailgating, a type of breach involving social engineering. Having already implemented training on how to spot Tailgating, Preston was looking for ways to further improve their approach.
SEE ALSO: Discussing Email DLP over Dinner with Preston Terada
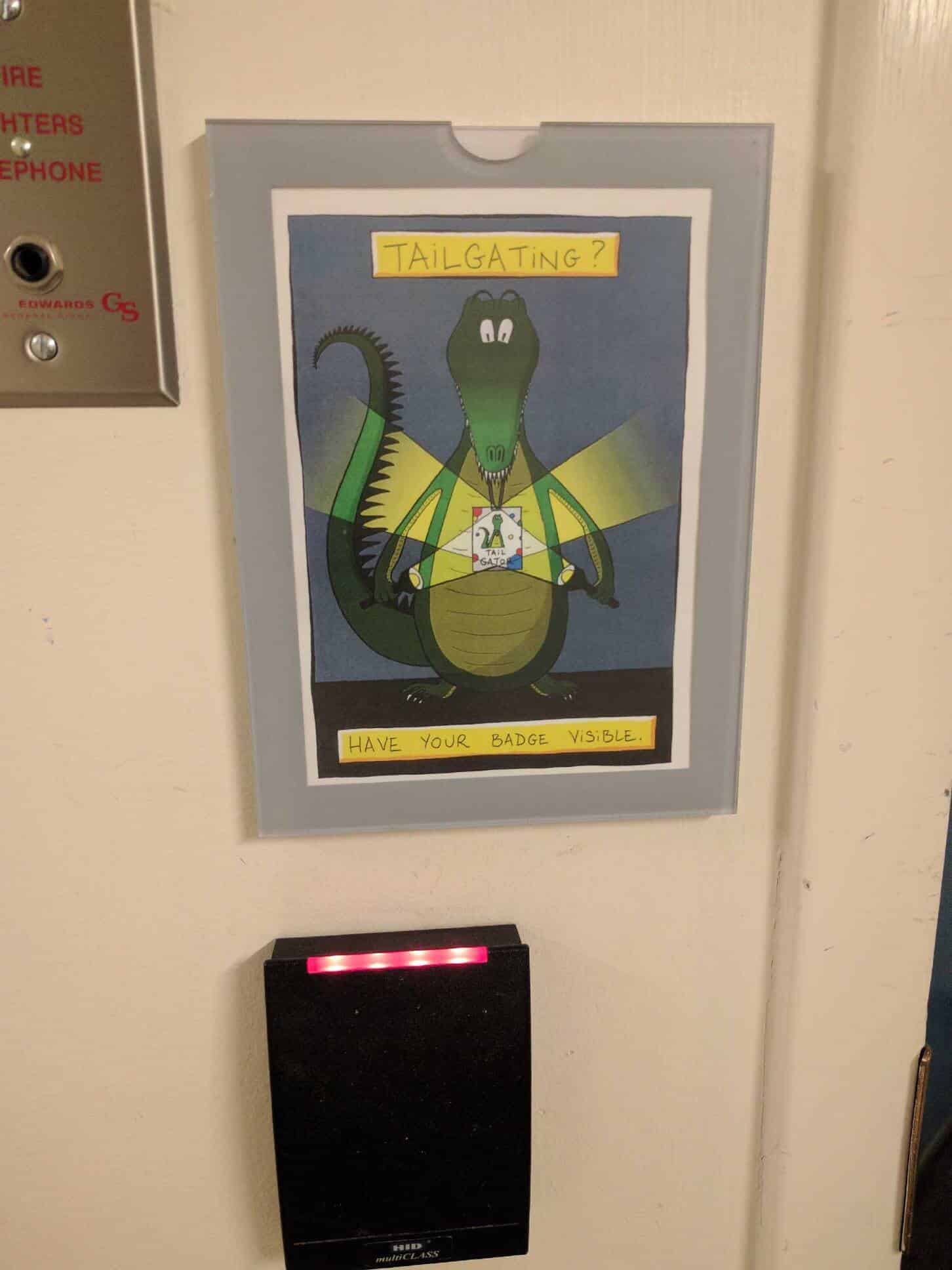
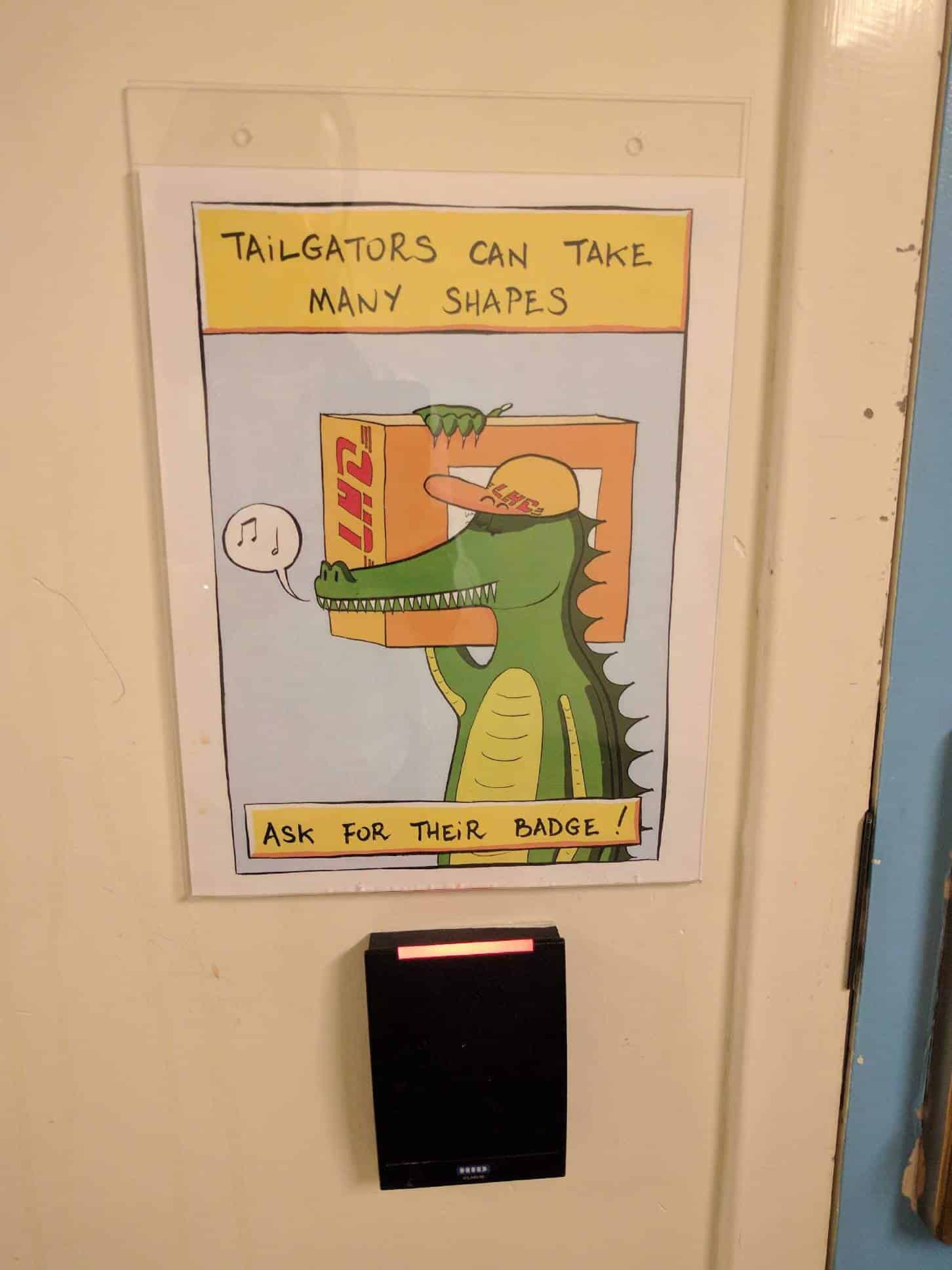
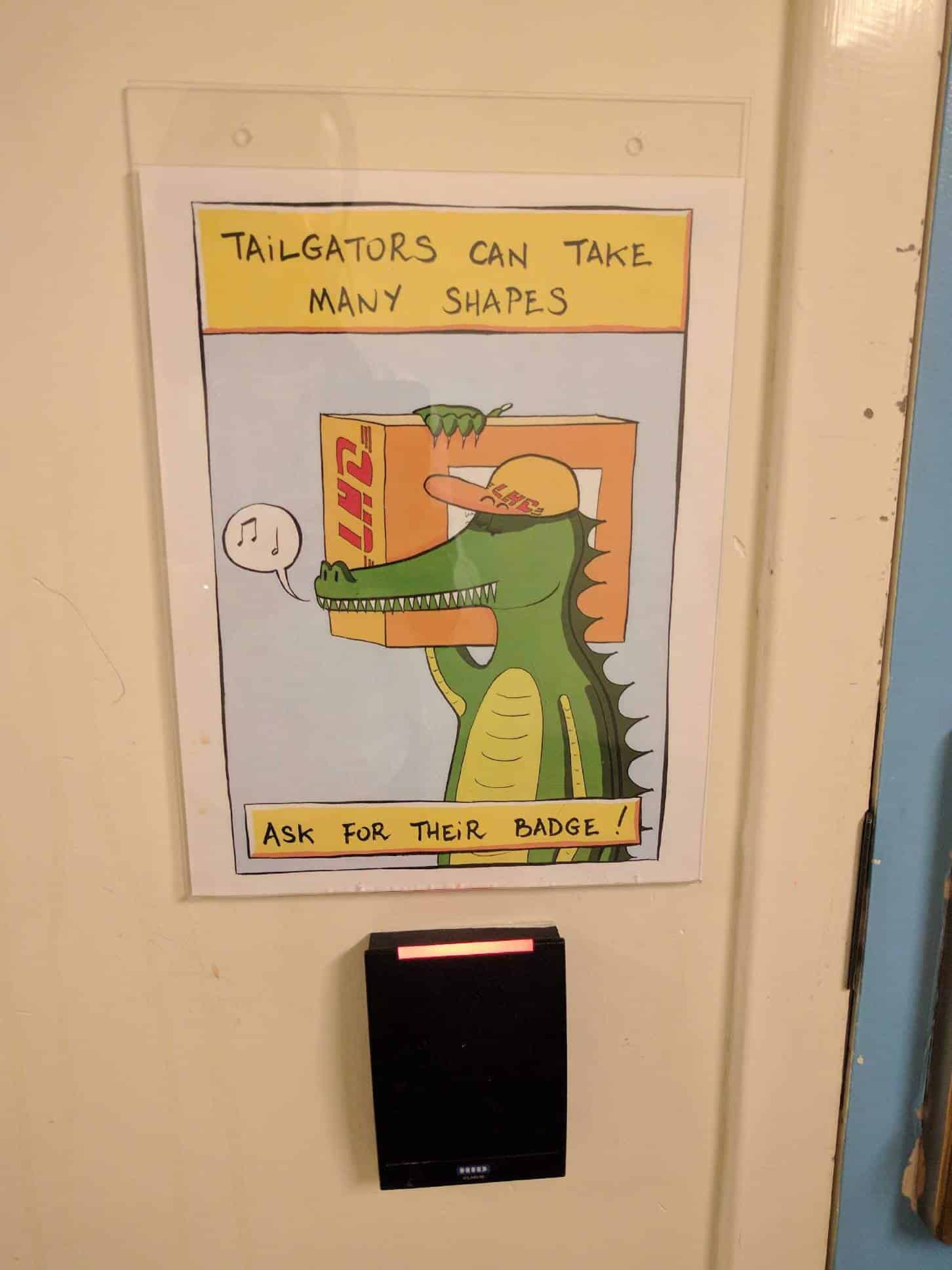
Tailgating or “ piggybacking,” is a social engineering attack that occurs when someone who lacks proper authentication follows an employee into a restricted area. A good example would be simply walking behind the person who has access to a resource. Out of social courtesy, the legitimate user may hold the door open for the attacker. In a slightly more sophisticated approach, an attacker impersonates a delivery driver and waits outside a building or a door. When an employee opens the door with their badge, the attacker asks them to hold the door while they carry their package(s) in. Tailgating does not work in all corporate settings however. In larger organizations, all persons entering a building are required to swipe a card. In mid-size enterprises, attackers can strike up conversations with employees and use this show of familiarity to successfully get past the front desk. Performing ongoing Employee HIPAA Training can greatly mitigate chances of a HIPAA Violation occurring due to Tailgating. This is precisely what Kahala Nui does.
SEE ALSO: One Major Part of HIPAA You May Be Missing
Every Friday we bring you the most important news from Paubox. Our aim is to make you smarter, faster.