Last week I wrote about the problem with Display Name Spoofing in email security, why you should care, and what we're doing about it.
Based on feedback we've gotten since then, a second post on the topic is needed.
Phishing is a Top Breach Risk

Gibson's Bar & Steakhouse in Chicago
Last week Greg Hoffman and I flew to Chicago to present to a dozen executives in the dental industry.
In a conference room at the tony Waldorf Astoria, I shared with them:
- Our unique approach to secure email
- Our commitment to security via the HITRUST RightStart program
- How the incumbents have failed to deliver a viable solution thus far
- Traction and plans for the future
Later in the day, we caught up with a CIO of one the large dental associations we presented to. As we shared how Paubox is delivering value to the market, we got on the topic of phishing attacks via Display Name Spoofing. He mentioned all of his peers in the industry are currently experiencing this problem. That viewpoint matches the data we've compiled via our monthly HIPAA Breach Reports.
In a nutshell, email breaches have been the primary HIPAA breach point for 2019 and most of 2018.
See also: HIPAA Breach Report for June 2019
He also shared this with me: “At the end of the day, our top risk is being phished. That’s gonna lead to a breach.”
In short, Phishing is a top breach risk in healthcare.
A Solution to Display Name Spoofing Attacks
Here's how we solved Display Name Spoofing attacks with Paubox Email Suite Plus.
Step 1. We work with our customers to get a list of the C-level executives being impersonated within their organization. This would include their names and email addresses they use to communicate with staff.
Step 2. We add those entries into our Display Name Spoofing protection database.
Step 3. If an email comes in that matches a name on the Display Name Spoofing protection list and does not match an email tied to it, the email is immediately quarantined. This approach prevents the malicious email from reaching the end user's inbox.
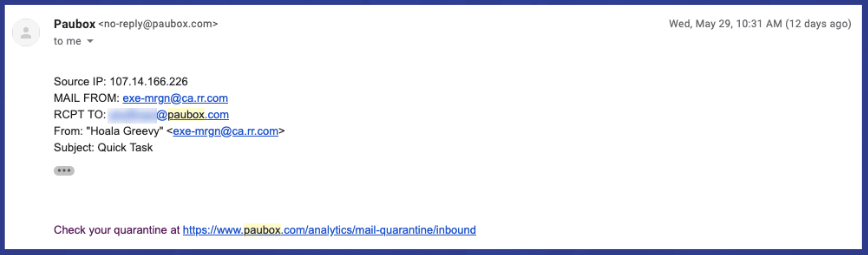
Step 4. We send an email notification to the customer admin(s) notifying them we've stopped a Display Name phishing attack. It's simple, effective, and it works.
See Related: US Patent Office Approves our Approach to Display Name Spoofing
Subscribe to Paubox Weekly
Every Friday we bring you the most important news from Paubox. Our aim is to make you smarter, faster.

 Hoala Greevy
Hoala Greevy