The FBI’s recent ransomware warnings are ominous indicators of cyber concerns that organizations face in 2020. Less than a week after issuing warnings against LockerGoga and MegaCortex, the FBI’s latest alert cautions the private sector about Maze ransomware.
Maze ransomware – distinctive and harmful
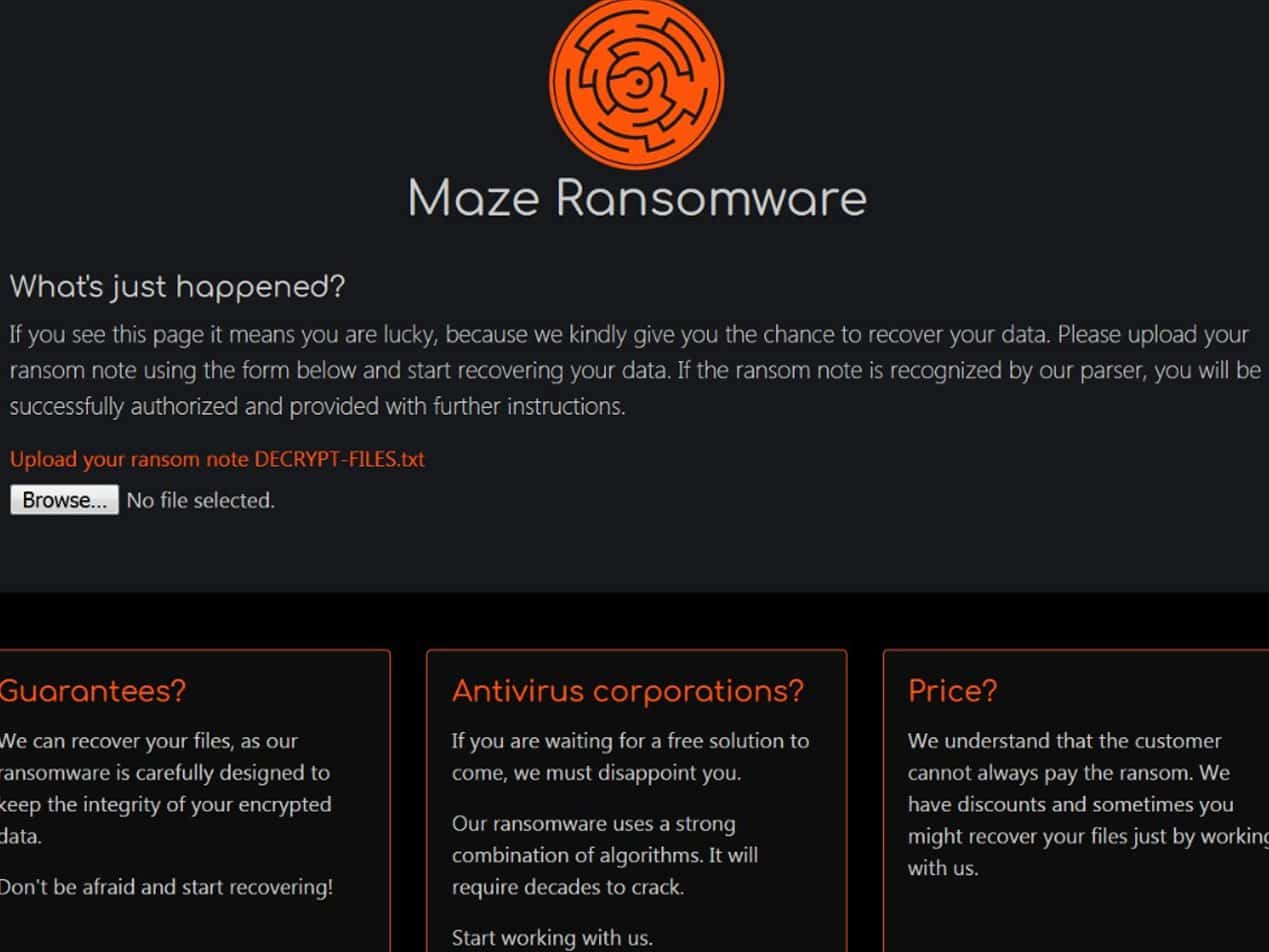
Maze ransomware, first observed in the U.S. in November 2019, differs from common ransomware that only encrypts data before hackers demand money for a decryption key. The Maze hackers first exfiltrate or steal data as ransom insurance, what ZDNet is calling a new pay-or-we-will-leak-your-data approach. Thus far Maze is the only group known to publicly release data, but with other ransomware groups—such as REvil (Sodinokibi), Zeppelin, and Snatch—following their lead, the possibility of this happening more is obvious. Both the City of Pensacola and Southwire, a manufacturing company, did not pay and had portions of their stolen data released online. Southwire is in the middle of a civil suit against the unknown Maze group.
To pay or not to pay?
The current trend is for organizations to pay the ransom even though the FBI, the Department of Health and Human Services, and security professionals advise against it. Victims, particularly healthcare organizations, must weigh the cost of paying the ransom versus the public disclosure of confidential, sensitive information. Unfortunately, there is no guarantee that a decryption key will be provided. No indication that the hackers will not demand more money. And in the case of Maze, there is no guarantee that the stolen data won’t still be released. Further guidance and studies are needed.
How can you not become a victim?
Avoid becoming a target by planning and utilizing strong security measures. Start by checking every device within your network for vulnerabilities and update your systems and your software. Separate important, sensitive information from everything else. For healthcare, ensure you use HIPAA compliant email. Utilize offline backup, multi-factor authentication, and email security software such as Paubox Email Suite Plus. Finally, educate those within your organization about good computing habits, starting with the use of strong passwords and including how to recognize and block malicious emails. Hackers attempting to breach your organization may be inevitable but breaches are preventable if you spend the time and energy to secure a strong security program.
Subscribe to Paubox Weekly
Every Friday we'll bring you the most important news from Paubox. Our aim is to make you smarter, faster.