The FBI is investigating a cyberattack that has left the University of Vermont (UVM) Health Network unable to operate fully for over a month.
The FBI is investigating a cyberattack that has left the University of Vermont (UVM) Health Network unable to operate fully for over a month.
What happened?
On October 28th, the hospital IT staff shut down its network after noticing unusual activity. The network shutdown meant that hospital operations could no longer use email, access patient records, and it delayed billing statements and payment processing. Even though UVM has made some progress in recovering its network server, the team believes it will be several weeks before operations will run as usual. UVM Health Network or the FBI hasn’t commented about what caused the network outage, but reports suggest that the attack happened through the hospital’s central computer server and spread through the IT network. At this time, there aren’t any reports of protected health information ( PHI ) misuse.How has the cyberattack affected the UVM Health Network?
UVM Health Network has had to make significant changes to continue to provide quality, but limited, care to its patients. Staff have had to switch to paper medical records, and they were unable to access online patient medical history, appointments, or medications. Patients’ well-being has been greatly affected by the network shutdown. The hospital couldn’t schedule appointment times at first and had to delay potentially life-saving treatments and screenings like chemotherapy, mammograms, and biopsies. As the network shutdown continues, The UVM Health Network has left many patients in the dark about when they can come in again for their appointments. The cyberattack also impacted employees. Up to 300 team members are reassigned or furloughed while the network is down.A rise in healthcare cyberattacks
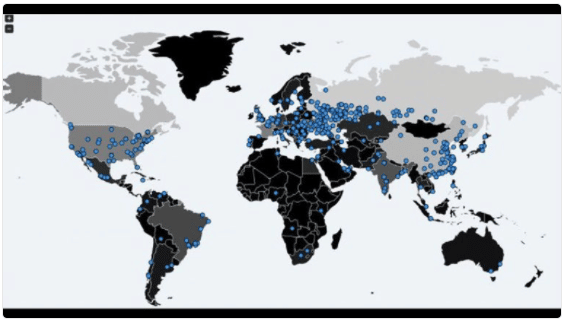
The cyberattack on UVM Health Network is part of a growing trend of attacks on healthcare providers. In Q3 2020, ransomware attacks saw a global surge , with the healthcare industry being the most impacted. There was a ransomware victim every 10 seconds in Q3. SEE MORE: Coronavirus Cyberattacks: How to Protect Yourself Cybercriminals often participate in schemes known as a double extortion attack . Hackers will try to get their victims to pay a ransom for two separate assets. The first ransom is to unencrypt the stolen data and return it to the victims. The second ransom is to prevent healthcare data from leaking onto the dark web. Double extortion attacks are costly, especially when you add in hefty fines for violating HIPAA . It’s far cheaper to keep your IT system updated and prepared for a potential cyberattack. SEE MORE: The Costs of Ransomware AttacksHow Paubox can help prevent cyberattacks
Al Gobeille, vice president of operations at UVM Medical center, has said that part of the company’s recovery process included making its IT system more secure. The company has already upgraded its email system after the attack which is a good move because email is the number one threat vector for cyberattacks. It only takes one employee to click on one link for hackers to enter your network and wreak havoc on your operations. Training your employees is a fundamental part of keeping your network safe. But you also need to protect your healthcare data against human error proactively. SEE MORE: Hacking and Human Error: Two Enemies of HIPAA Compliance Paubox Email Suite Plus enables you to send HIPAA compliant email while also providing robust inbound security. Our security tools block email threats from reaching your inbox and are an effective safeguard against human error. It would be best to consider upgrading your email security before hackers discover that you have a vulnerability.Subscribe to Paubox Weekly
Every Friday we'll bring you the most important news from Paubox. Our aim is to make you smarter, faster.