3 min read
Watering hole attack: What it is and how to protect against it
Rick Kuwahara January 26, 2020
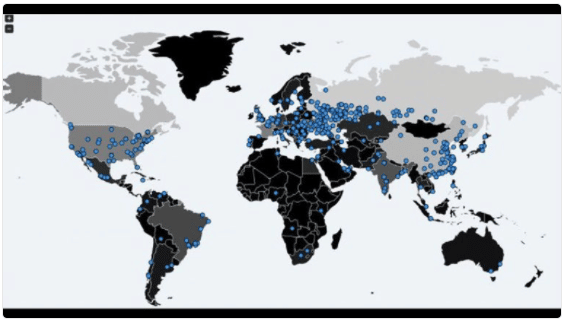
Cybersecurity researchers from Kaspersky Labs recently uncovered a country-level watering hole attack targeting a central Asian country’s national data center . The hacker group called LuckyMouse wanted to gain access to government resources and has been behind many previous cyber attacks that have resulted in the theft of massive amounts of data. The most targeted groups for watering hole attacks are government agencies, regulatory bodies, financial authorities, and compliance professionals because cyber criminals can steal corporate network credentials to stage a lateral attack within an organization.
What is a watering hole attack?
Watering hole attacks (also known as strategic website compromise attacks) are designed to compromise a specific group of end users (often employees of large enterprises) within a particular industry through popular websites. The primary aim is to infect a user’s computer with malicious code to get access to the network at the user’s place of employment. Compromising legitimate industry websites, such as conferences, standards bodies, and professional discussion boards is a common practice. Once a website is infected, cyber criminals will lure visitors to the compromised websites by sending spear phishing emails that direct them to certain areas of the site. The name of the cyber attack is inspired by animal predators who lurk near watering holes looking for the chance to attack their prey. Once their prey visits the “watering hole” the user’s browser will download malware from the infected website without the user’s knowledge. This allows cyber criminals to steal the end user’s corporate network credentials and stage larger targeted attacks within the user’s organization.
How to prevent watering hole attacks
Malware solutions are the first line of defense against watering hole attacks. Web gateways can also provide some detection capability of drive-by downloads that match a known signature or bad reputation. Enterprise organizations should also consider more advanced malware solutions that look for malicious behavior on popular websites that users frequently visit. An email security solution that has advanced malware analysis during email delivery can help an organization defend against targeted email lures to “watering holes”. The email solution should protect the user when they are and aren’t on the corporate network. Organizations can also run web browsers in virtual environments that limit the connection to production systems or use virtual containers to limit access to the local system. Virtual environments can also be used just for browsing to websites that may be used in a watering hole attack or for other interactions with untrusted systems. A secure cloud browser can avoid processing web content locally and provide complete anonymity to its users with a clean slate for each session. The most commonly targeted software for watering hole attacks is Flash, Adobe Reader, Microsoft's Internet Explorer, and Java Runtime Environment (JRE). Organizations can remove or disable these programs to prevent watering hole attacks.
How to protect your organization from an attack
Once malware is in a browser, it can access whatever the browser can, even if it is in a virtual environment. It can undertake a variety of malicious activities, including encrypting the user’s data and requesting a ransom to recover it, capturing IDs, passwords, and payment card data, and stealing sensitive data from the user’s employer. Deploying advanced network security monitoring tools and behavioral analysis can help detect zero-day vulnerabilities and exploits. Such attack threats use previously unknown tactics that are difficult to identify with traditional signature-based controls that rely on the knowledge of past threats. Behavioral analysis software can spot unusual user behavior like a user’s machine sending confidential documents after regular business hours. Advanced malware detection technologies can perform deep content inspection of suspicious websites or code to identify malicious behaviors before they cause more damage. It’s essential that organizations treat all third-party traffic as untrusted until verified, whether it’s from an inconspicuous partner website or a popular consumer website. A security solution that inspects all network traffic, including SSL-encrypted traffic, is essential to pinpointing traffic resulting from a watering hole attack. Training employees and educating users with access to critical data and infrastructure about watering hole attacks can go a long way towards preventing and protecting your organization from attackers. Updating software promptly, especially with the latest security patches can also lessen your organization’s risk.
Conclusion
Awareness training combined with solid security systems will help lay the foundation for defending your organization against increasingly sophisticated hacking methods such as watering hole attacks. But although an employee can be trained to recognize an email phishing attack, there currently isn’t an easy way for an employee to identify compromised but legitimate websites. This is when the security systems you have in place should step in to bridge the gap to keep your organization protected.
Additional Reading: HIPAA Compliant Email: The Definitive Guide
Subscribe to Paubox Weekly
Every Friday we'll bring you the most important news from Paubox. Our aim is to make you smarter, faster.