The costs of ransomware attacks can be detrimental, especially to organizations in the healthcare industry, working daily with sensitive, protected health information (PHI). Let’s explore the current issues with and costs of ransomware as well as measures covered entities should take to safeguard themselves.
What is ransomware?
In a 2016 blog post, we called ransomware “the biggest threat to email security in healthcare”—this is still accurate today.
RELATED: INTERPOL Warns of Increased Ransomware Attacks on Hospitals
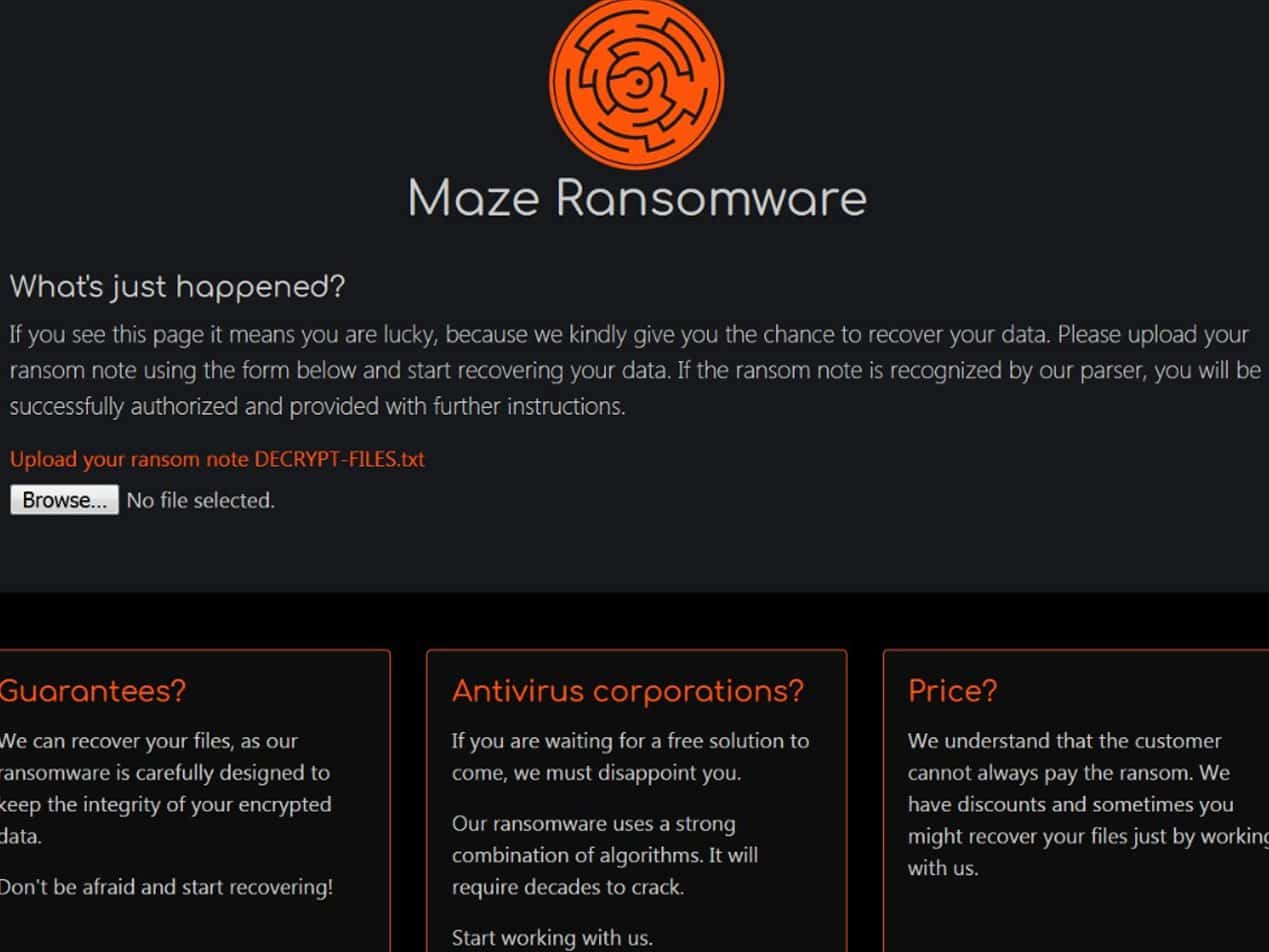
Ransomware is malware (or malicious software) used to deny a victim access to a system until a ransom is paid. Victims can download malware through phishing emails that include malicious attachments or fraudulent links. A simple click can give a hacker access to data for encryption and ransom. Rangely District Hospital (RDH) in Colorado, for example, recently had software encrypted by hackers due to a successful ransomeware attack, which blocked patient records and possibly exposed PHI. Typically, threat actors stop at encryption; however new groups, such as the Maze ransomware group, also exfiltrate and leak data to force bigger payoffs. Others are even adapting their strategies to take advantage of the coronavirus pandemic, launching malware immediately to extort an overwhelmed covered entity.
What are the costs of a ransomware attack?
The immediate cost of a ransomware attack is obvious: the inability to access encrypted data. Problems can develop from this if the encrypted data is sensitive or essential, or if a backup does not exist or ends up encrypted as well. A second direct cost occurs if the cybercriminal exfiltrated the data before encryption. The threat actor may publicly release PHI or sell it to other cybercriminals for further ransom or exposure.
RELATED: Horror Stories: When Cybercriminals Attack Hospitals
A third cost relates to possible HIPAA violations due to a cyberattack. After a breach, a covered entity must submit a notice to the U.S. Department of Health and Human Services (HHS), affected parties, and the proper authorities. Depending on the outcome of the HHS Office for Civil Rights compliance review, the covered entity may have to pay a fine (sometimes astronomical) and put a corrective action plan into place.
RELATED: Healthcare Provider Pays Hefty Settlement for HIPAA Noncompliance
Finally, further monetary costs may arise, immediately and in the future, depending on if a ransom is paid or not.
To pay or not to pay?
In reality, the costs of both refusing to pay and paying a ransom can be high. This includes monetary costs related to recovery, such as decrypting data and rebuilding safeguards (especially relating to HIPAA compliant email), as well as damages to a reputation. Not all covered entities can pay a ransom (some even choose to shut down instead) while others decide that paying isn’t possible or helpful; for example RDH did not pay and is still unable to access its encrypted files. And those that end up paying the ransom may not be given a workable decryption key or worse—they may be asked to pay more. Lastly, chances are a covered entity will face another breach, particularly if the organization becomes known for weak security or paying ransoms. To pay or not to pay is a hard decision, which is why prevention strategies must be in place to avoid ransomware attacks and costs.What stops ransomware?
RDH unfortunately lacked a strong backup and email security plan, both essential to stop the consequences of ransomware along with up-to-date employee awareness training. Furthermore, utilizing an email security service, such as Paubox Email Suite Plus, stops malware from even reaching a user’s inbox. If a cybercriminal attempts to breach your system, Paubox can isolate and block the problem before it causes irreparable problems. In short, it is worthwhile to invest time and effort in strong, layered security measures to keep ransomware costs from dismantling your organization.
Subscribe to Paubox Weekly
Every Friday we'll bring you the most important news from Paubox. Our aim is to make you smarter, faster.