
Last August, we wrote a post called Display Name Spoofing attacks via LinkedIn. In it, we identified a new variant of Display Name Spoofing phishing attacks- the abuse of LinkedIn to build a social construct of manipulation. Our contention, dating back to August 2020, was that LinkedIn was being scraped at scale for Display Name Spoofing attack campaigns. Yesterday's news proves we were right:
- Details On 700 Million LinkedIn Users For Sale On Notorious Hacking Forum (Forbes)
- 700m LinkedIn records up for sale on the underground hacking forum (TechRadar)
- Data from half a billion LinkedIn users has been scraped and put online (Fortune)
This post recaps how we arrived at our conclusion nearly a year before anyone else caught on.
Display Name Spoofing: Manipulating Authority and Smartphones
As a recap, Display Name Spoofing is a phishing attack that appears to come from a person of authority within a company. When this is coupled with the:
- At least 70% of all email is now read from a smartphone.
- By default, email apps on a smartphone only show the Display Name of the sender. If you want to see the actual email address, further action (i.e., friction) is required.
The net effect is that if you see an email from your boss on your phone, you’ll probably open it immediately, not bothering to think about the actual email address it came from. In essence, Display Name Spoofing attacks tend to work because they manipulate the following:
- Corporate hierarchy
- How employees check email
- Inherent shortcomings of today’s smartphones
Scraping LinkedIn at Scale
In today’s society, people keep their LinkedIn profiles studiously current. Job title and current employer are especially manicured on LinkedIn. In fact, it’s what makes LinkedIn such an effective platform for Outbound Sales Development. With LinkedIn, you know where everyone works and where everyone sits in the org chart. While not an epiphany, that last sentence profoundly affects email security.
ExecProtect Provides the Proof
Within our 40-person startup, we’ve seen ample proof of LinkedIn being abused for phishing attacks via Display Name Spoofing. Last year, for example, ExecProtect stopped the following phishing attack dead in its tracks:
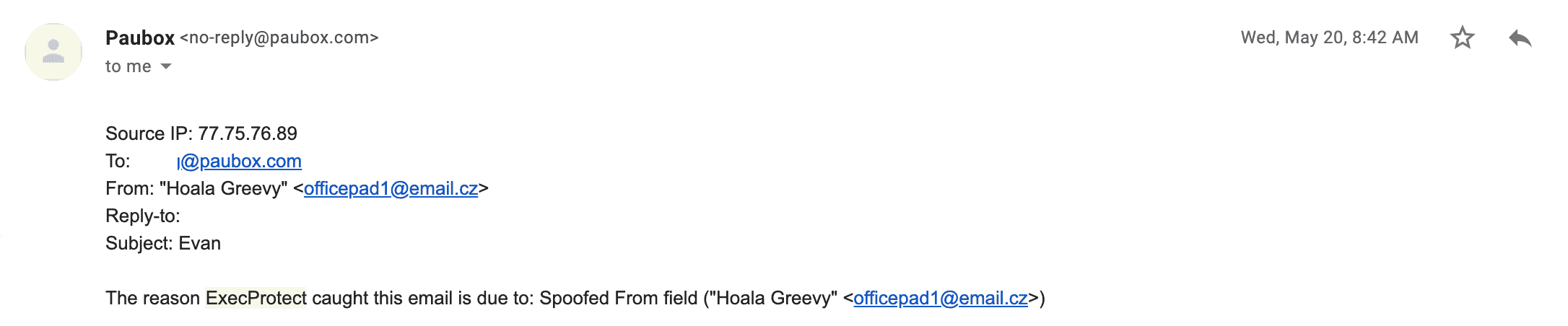
The above screenshot is an alert email ExecProtect sends to Domain Administrators like me. At a quick glance, we can see that:
- An email was sent to a Paubox employee, Evan, supposedly from me, the CEO.
- I obviously do not have an email address of officepad1@email.cz, and ExecProtect instantly quarantined it. Don't forget, though; it's challenging to realize this on a smartphone.
- The IP address that sent the email, 77.75.76.89, was not on any RBL Blacklists. In other words, the IP was recognized as a legitimate sender.
Here's the smoking gun: Evan did not even work at Paubox yet! In reality, he was so fired up to start that he updated his LinkedIn profile six days before his start date. LinkedIn was the only way to know that Evan had a connection to Paubox at that time. There were other times when ExecProtect would stop dozens of Display Name Spoofing attacks in the span of two minutes. The entire company was targeted all at once, with the hope of at least one hit.
See Also: US Patent Office Approves our Approach to Display Name Spoofing
Sound familiar? In these instances, it's hard to find a one-to-one correlation to LinkedIn, as company directories can be purchased from other sources. However, the same cannot be said when an employee is targeted and hasn't even started work yet. In our case, there was only one place that information existed- on LinkedIn.
If a company of our size was targeted with pinpoint precision, yesterday's news correctly concluded that the same is true for every company on LinkedIn.
Subscribe to Paubox Weekly
Every Friday we'll bring you the most important news from Paubox. Our aim is to make you smarter, faster.



 Hoala Greevy
Hoala Greevy

