3 min read
GitHub leaks healthcare information - HHS still likely unaware
Chloe Bowen August 21, 2020
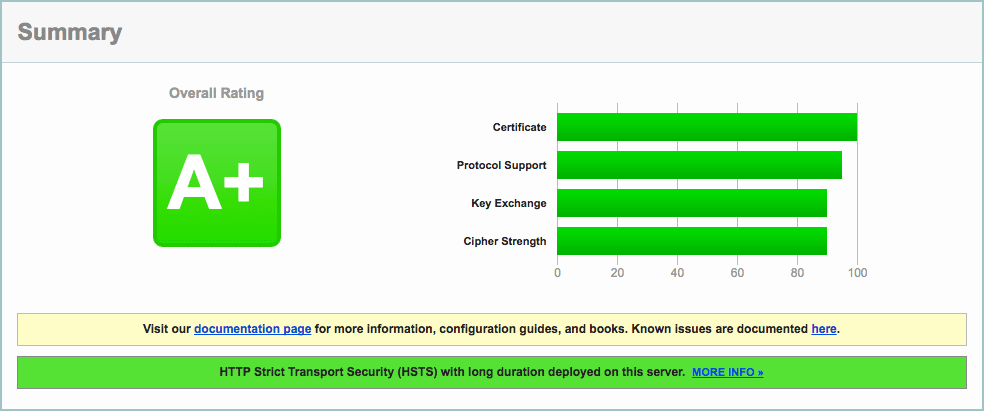
As an email vendor for healthcare providers, security is built into Paubox’s everyday practices. After all, HIPAA compliant email is the cornerstone of our business. Unfortunately, we cannot say the same thing for all business associates and covered entities . On Monday, Databreaches.net and security researcher Jelle Ursem came out with a report that detailed an incident where the protected health information (PHI) of 150,000 to 200,000 individuals was leaked on GitHub. It is not known if this data breach has been reported to The U.S. Department of Health & Human Services or state regulators yet, or if the individuals affected have been notified.
What is GitHub?
GitHub is a hosting platform where code can be stored or shared between developers and teams. While code can be stored in public for use by other developers, enterprise systems and corporations will typically choose to store code privately due to the sensitive nature of their data.
So what happened?
In the case of these data breaches, Dutch security researcher Jelle Ursem discovered two major mistakes when he decided to check if any healthcare providers had stored medical information on GitHub . In Paubox’s latest HIPAA Critical podcast, Paubox CEO Hoala Greevey noted that Ursem found two places where 9 U.S. healthcare entities involved in this breach made mistakes.
- Developers hardcoded employee login credentials into the code rather than separating them out.
- Developers had uploaded the code into public GitHub repositories for anyone to download and use.
“So in other words,” Greevy explained, “username and passwords are there on GitHub for anyone to see, and apparently, [Ursem] started finding these things within 10 minutes of searching.” If you didn’t know before, hardcoding is the practice of embedding data directly into a program's source code as opposed to obtaining the data from external sources. In several of the GitHub breach cases, developers working with covered entities and business associates had entered employee login credential data into the original program source code. This could allow any GitHub user to simply obtain access to, for example, Microsoft 365 email accounts which would then give them access to swathes of patient data. If that isn’t horrifying enough, think of this: In some cases, those employee credentials had been available for the entire world to see and download from public GitHub repositories for the past three years! “This is why we’re so tightly aligned with HITRUST ,” Greevy noted. “We really like what they’re doing. And it validates our approaches to security. So when we went through our recertification process this year . . . one of the many hundreds of controls we had to prove was that we do not co-mingle, user logins in our source code.”
Why this breach matters
Failing to audit a developer's processes, third-party or not, puts covered entities at risk for millions of dollars in fines due to a HIPAA violation. Knowledge of a data breach requires you to take the necessary steps to either cure the breach or terminate the contract with your business associate . A hardcoded login credential can allow even the most unskilled hackers to log into company software and extract hundreds of thousands of patients’ data for malicious purposes like identity theft and credit card fraud. Luckily the researcher in this case caught the oversight prior to any criminals who could have used the breached data to dig even deeper into the corporations involved.
The Paubox difference
While the data breach in this report might seem like an extreme case of negligence, the fact that it only recently came to light showcases that some vendors still have a long way to go in the realm of PHI security management. Paubox seeks to be a trailblazer and model for how business associates can responsibly store PHI. “When we went through our recertification process this year [with HITRUST ], one of the many hundreds of controls we had to prove was that we do not co-mingle user login in our source code,” Greevey said when describing what it has taken for Paubox to become a leader in HIPAA email security. The practice of login commingling is a specific violation of 12-Factor App configuration. This kind configuration is required for HITRUST certification, and it is the configuration that Paubox employs. In fact, the 12-Factor App development methodology is core to Paubox, and any violation of it would compromise the service. HIPAA compliance is baked into what Paubox does, and it wouldn’t be the company it is without it.
Looking ahead
Patient data security in the cloud is an urgent matter. With sensitive data like patient diagnoses, insurance information, provider data, and third-party business contracts at stake, the need for tough security measures is absolutely paramount to avoid the catastrophic consequences that could arise from malicious actors. Make sure you vet your business associates and their commitment to security before working with them. The digital transformation in healthcare is opening up a sea of possibilities for healthcare organizations. Just behind its wake lies the opportunity for bad actors. Partner with a company like Paubox to ensure you are benefiting from new technology while maintaining safe, secure, and HIPAA compliant business practices.
Subscribe to Paubox Weekly
Every Friday we'll bring you the most important news from Paubox. Our aim is to make you smarter, faster.