 That’s a wrap on Paubox SECURE @ Home 2020! A special thank you to all attendees, panelists, and of course, our sponsors, HITRUST , BEYOND LLC , Goodwin , and HIPAA Ready . Don’t worry if you missed a panel from today or yesterday; you can still upgrade to a premium registration to gain access to recordings of all panel sessions. Day 2 saw panels from industry leaders like Kelvin Coleman , executive director at the National Cyber Security Alliance , and James Plouffe , senior partner solutions architect at AttackIQ . Here’s a recap of today’s panels. Click here to register for access to all panel session recordings.
That’s a wrap on Paubox SECURE @ Home 2020! A special thank you to all attendees, panelists, and of course, our sponsors, HITRUST , BEYOND LLC , Goodwin , and HIPAA Ready . Don’t worry if you missed a panel from today or yesterday; you can still upgrade to a premium registration to gain access to recordings of all panel sessions. Day 2 saw panels from industry leaders like Kelvin Coleman , executive director at the National Cyber Security Alliance , and James Plouffe , senior partner solutions architect at AttackIQ . Here’s a recap of today’s panels. Click here to register for access to all panel session recordings.
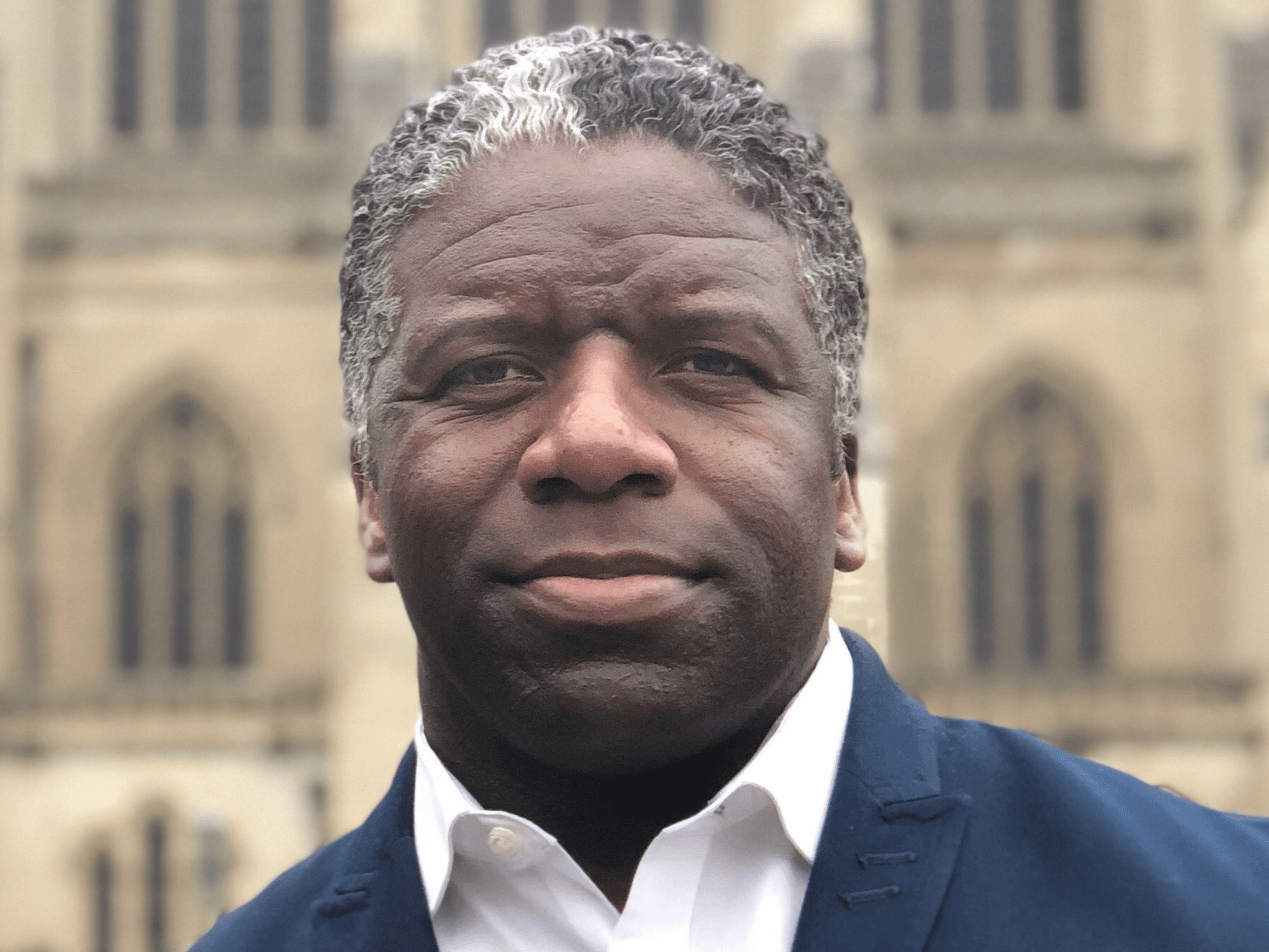
Security Awareness with a Remote Team | Kelvin Coleman
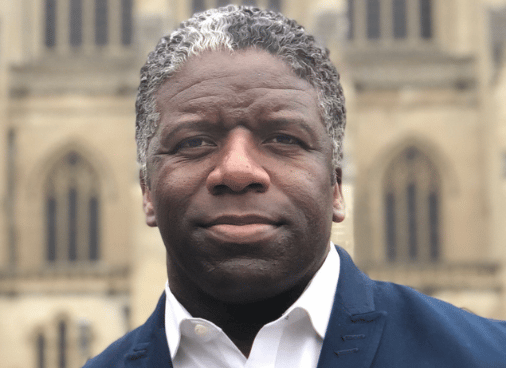
Panel overview: An increase in telecommuting
gives cyber criminals more opportunities to exploit unprotected threat vectors . The best-laid security plan can fall apart when individuals are exploited through phishing emails , social engineering, and related efforts. This is why understanding cybersecurity is as important as using cybersecurity. SEE ALSO: Cybersecurity Challenges of Remote Working Key takeaways:
- Passwords are essential, but multi-factor authentication is more important. Think of passwords as keys, and multi-factor authentication as a deadbolt lock.
- Don't put more information online than you have to. Keep it at a bare minimum, especially with personally identifiable information (PII).
- Email phishing social media phishing (like through LinkedIn) is still a top threat that people fall victim to every day.
Third Party Risk Management in a COVID World | Melissa Bendana & Marc Haskelson

Panel overview: This panel explored the
complexities and importance of third-party security in 2020, especially in a COVID-19 world. Key takeaways:
- It can be easy to focus on a computer’s security, but users must consider the security of other, easily accessible technologies too, such as a printer.
- People should consider using a VPN, adding a password to their Internet network, changing the default password on their wifi modem, and adding a guest wifi network for added security.
- Organizations need to not only have a business continuity plan but test it as well.
Transitioning From Legacy Systems to the Cloud for Better Security | Dave Ledoux
Panel overview: An important part of the
healthcare digital transformation is moving from on-premises solutions to the cloud, but sometimes the challenge can seem so large that it’s hard to know where to begin. Key takeaways:
- IT security needs to be a frictionless experience for all, especially the end-user.
- Migrating to the cloud can help a company implement automatic workflows, saving time and effort.
- Nizhoni was in an excellent position to transition to remote work due to the coronavirus pandemic because it had already transitioned to the cloud.
- The company has saved both time and money; phasing out the fax machine alone has saved thousands of dollars a year.
Embracing Zero Trust (When You Aren’t the World’s Largest Internet Company) | James Plouffe
Panel overview: Zero trust is a mobile-centric
security concept that centers around device validation, app authorization, and network verification before a network connection is granted. All of this helps with endpoint security so your organization remains secure from outside attackers while maintaining HIPAA compliance. Key takeaways:
- A zero trust infrastructure is not a fork-lift upgrade; many organizations already have many of the building blocks.
- Organizations must strengthen their authentication practices and complete an inventory of all endpoints and services.
- Reference documents and architectures present some components of zero trust as uniform across the board. However, in practice, many aren’t.
Usable Security: A Human-Centric Approach to Security | Julie Haney & Andrew Hicks

Panel overview: Usable security is the
intersection of cybersecurity, human factors, and human-computer interaction. The idea is to positively influence cybersecurity standards and guidelines while also improving usability, which is why the need for usable security and compliance go hand-in-hand. Key takeaways:
- Security buy-in takes time and effort from the top down (executives to employees).
- Security should drive initiatives with compliance elements weaved in.
- Usability and security need to coexist. Organizations should take the burden of security away from end-users and not expect them to be perfect.
About Paubox SECURE @ Home
Paubox SECURE @ Home is a virtual healthcare cybersecurity and innovation conference, bringing together industry leaders in a unique event to drive learning and discussion around the challenges of driving innovation in healthcare while keeping data secure. Upgrade to a paid registrants today to receive access to recordings of all live panels. Are you considering a HIPAA compliant email solution? Try Paubox Email Suite free today for 14-days.Subscribe to Paubox Weekly
Every Friday we'll bring you the most important news from Paubox. Our aim is to make you smarter, faster.