
HITRUST Fatigue set in last night at the office as we worked on punching out our HITRUST assessment. Tyler "Commish" Dornenburg and I put in a robust 14 hours on HITRUST yesterday. Well, more like I did 13 hours and he did 14. I went down for a power nap for a bit. Working six days a week to kick off 2019 is a part of our journey along the HITRUST RightStart program. This post is another behind the scenes (BTS) look at a startup striving for HITRUST certification.
Getting Ready for the Final Round

Commish, Jonathan "BBQ" Greeley, Chris "Linux" Pearson, and I got on a Zoom call today to get on the page regarding our HITRUST progress. Here's what we covered during our meeting with Engineering:
- Getting on same page on screenshots and code samples as proof of implementation on controls
- Knocking out Section 10 - Password Management
- Knocking out Section 8 - Network Protection
As we entered a small conference room to put in work, BBQ remarked, "So are we getting ready for the final round?" Pretty classic M. Bison, Street Fighter II reference I'd say.
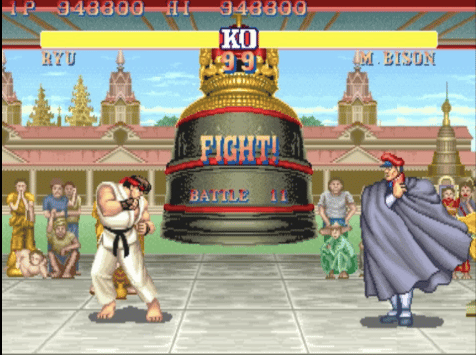
Getting ready for the final round
Configuration Management

I took a look at Section 6 - Configuration Management this morning and saw it had 16 controls remaining. That's where I extended my HITRUST efforts. Here's what I worked on within Configuration Management:
- Change Management policy and procedures
- Fallback Procedures for Change Management
It's 10:27pm now, I'm at home, working on more HITRUST controls. Uniquely tired. Forging ahead.
HITRUST
Founded in 2007, HITRUST Alliance is a not-for-profit organization whose mission is to champion programs that safeguard sensitive information and manage information risk for organizations across all industries and throughout the third-party supply chain. In collaboration with privacy, information security and risk management leaders from both the public and private sectors, HITRUST develops, maintains and provides broad access to its widely adopted common risk and compliance management and de-identification frameworks; related assessment and assurance methodologies; and initiatives advancing cyber sharing, analysis, and resilience.
Subscribe to Paubox Weekly
Every Friday we'll bring you the most important news from Paubox. Our aim is to make you smarter, faster.



 Hoala Greevy
Hoala Greevy


