3 min read
Chinese hackers use 4 zero-day exploits on Microsoft Exchange servers
 Hoala Greevy
March 06, 2021
Hoala Greevy
March 06, 2021
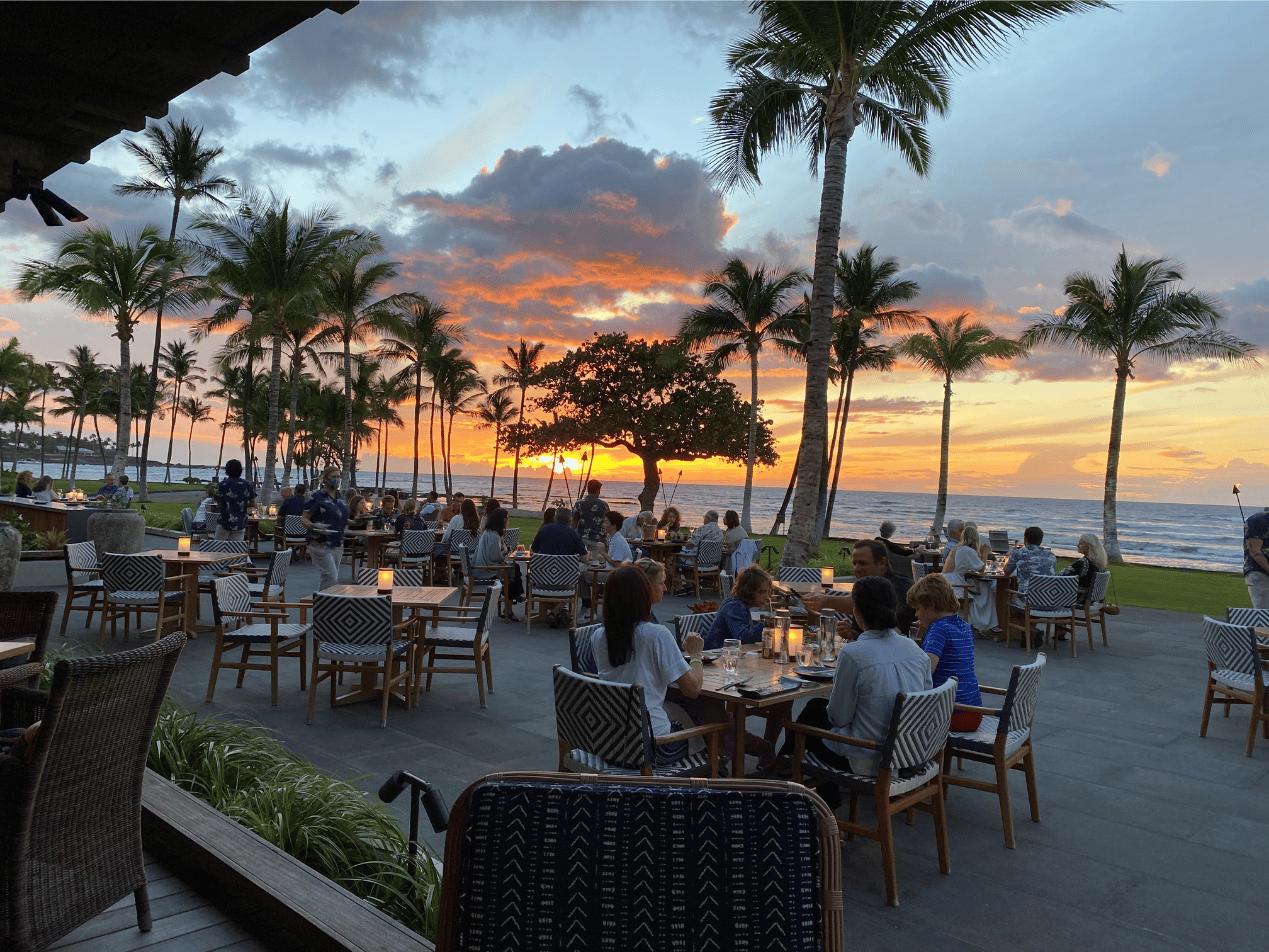
Yesterday as I settled down to a honeymoon dinner on the Kohala coast with my wife, I saw a notification on my iPhone: "China-Linked Hack Hits Tens of Thousands of U.S. Microsoft Customers." With early reports of 250,000 or more U.S. organizations running Microsoft Exchange being hacked, it was clear a quick response from us was in order. This post lays out the attack in simple terms, who is affected, and what to do about it.
SEE ALSO: Major Microsoft Exchange Hacks Spotted in the Wild
Who did it?
Earlier this week Microsoft's Threat Intelligence Center (MSTIC) described a new state-sponsored threat actor. They named the group Hafnium and called them "a highly skilled and sophisticated actor" operating in China. Hafnium is being attributed to this attack.How did it happen?
There were four zero-day exploits used as part of the attack chain. A zero-day is an unknown flaw in a system that's exploited before a fix becomes available from its creator. When multiple zero-days are strung together, it's called an attack chain. Also known as a cyber kill chain, an attack chain is a way to understand the sequence of events involved in an attack on an organization’s IT environment. All of the zero-days in this attack require the ability to make a connection to an Exchange email server on port 443 (HTTPS). It's important to note the attacks leveraged weaknesses in Microsoft's HTTPS port and not its SMTP port 25. If you are a Paubox customer running Microsoft Exchange that leverages our Inbound Security as part of Paubox Email Suite Plus or Premium, you'd know that we become the sole MX record for your organization's domain name(s). We also work with you to restrict incoming SMTP connections on port 25 so that they are only accepted from the Paubox platform. Due to the nature of Hafnium exploiting weaknesses in port 443 of Microsoft Exchange and not port 25, Paubox did not provide protection against this attack. As it stands today, it appears that if you run Exchange, the only way to have guarded against this attack was if:
- You never allowed Outlook Web Access (OWA) connections for your users in the first place. Since ActiveSync also runs on port 443, this is an unpopular/unlikely configuration.
- You required a VPN connection first in order to access OWA.
The Four Zero-Day Exploits
These are the four zero-day attacks used. It should be noted all of them used HTTPS port 443:
- CVE-2021-26855. This vulnerability in Exchange allowed the attacker to send arbitrary HTTP requests and authenticate as the Exchange server.
- CVE-2021-26857. Exploiting this vulnerability gave Hafnium the ability to run code as SYSTEM on the Exchange server.
- CVE-2021-26858. Once authenticated as the SYSTEM user, this vulnerability allowed arbitrary file write vulnerability in Exchange.
- CVE-2021-27065. This is another post-authentication arbitrary file write vulnerability in Exchange.
Affected versions of Microsoft Exchange
These are the affected versions of Microsoft Exchange:- Microsoft Exchange Server 2013
- Microsoft Exchange Server 2016
- Microsoft Exchange Server 2019
According to Microsoft, customers of cloud-based Microsoft 365 are not affected by this attack.
How do I update my Exchange Server?
The Microsoft post March 2021 Exchange Server Security Updates is a good place to start.
How do I know if my Exchange Server has been compromised?
Microsoft published a script on GitHub that can be used to detect if your Exchange server has been compromised. Volexity was credited by Microsoft for first reporting the vulnerabilities. According to Volexity President Steven Adair, "Even if you patched the same day Microsoft published its patches, there’s still a high chance there is a web shell on your server. The truth is, if you’re running Exchange and you haven’t patched this yet, there’s a very high chance that your organization is already compromised.”
What got stolen?
The attack was deployed in three phases:- First, access was gained to Exchange Servers via the aforementioned zero-day exploits.
- Second, web shells were installed. In a nutshell, web shells are backdoors that allow bad actors to steal data and perform further malicious actions.
- Third, the web shells were used to steal data from an organization's network. We've read reports of address books and entire email inboxes being surreptitiously uploaded to foreign networks.
Further reading:
Subscribe to Paubox Weekly
Every Friday we'll bring you the most important news from Paubox. Our aim is to make you smarter, faster.





