2 min read
Cybercriminals are adapting ransomware strategies to exploit the current crisis
Kapua Iao
May 26, 2020
Cybercriminals are adapting ransomware strategies to exploit the current crisis even further, according to Europol, the law enforcement agency of the European Union. Unfortunately, these cyber attackers are leveling their new tactics against hospitals and healthcare systems.
Adapting ransomware strategies
Ransomware is malicious software downloaded through phishing emails that allow a cybercriminal to infiltrate a system and steal data until a ransom is paid. Those affected are denied access to their system or have their data encrypted by the hacker. In 2019, there were reports of hackers, such as from the Maze ransomware group, using an exfiltrate then pay-or-we-will-leak-your-data approach. Depending on the circumstances, both the cost of refusing to pay and paying the ransom can be detrimental to organizations. This is especially true for healthcare struggling with safeguarding protected health information. Given the ongoing pandemic, several hacking groups, including Maze, publicly stated in March that they would not target medical organizations. While they (more or less) have stuck to their word, we are also seeing the opposite occurring. Recent Europol research shows that hackers are launching malware immediately if they determine the data is important.
Why now?
Worldwide security agencies, including INTERPOL, the U.S. Department of Homeland Security Cybersecurity Infrastructure Security Agency, and the U.K. National Cyber Security Centre, have sent out recent warnings about increased ransomware attacks. And at a recent United Nations meeting, the Security Council warned its members of a 600% increase in malicious emails. According to Fernando Ruiz Pérez, acting head of Europol’s Cybercrime Center, “Especially if the target is a hospital, government institution or a company operating online more than before because of the Covid situation, they know they have a good way to extort the company. They don’t even need to exfiltrate the data. They don’t need to wait.” Cybercriminals are banking on: 1) Overstressed employees more likely to click without thinking 2) Overwhelmed IT staff and lax cybersecurity 3) The need to have important stolen information back 4) Hospitals not having the time to negotiate or deny ransom payments. And early reports are showing that hospitals are paying the hefty ransoms. “As hospitals and medical organizations around the world are working non-stop to preserve the well-being of individuals stricken with coronavirus, they have become targets for ruthless cybercriminals who are looking to make a profit at the expense of sick patients,” said INTERPOL’s Secretary General Jürgen Stock.
Protection through strong cybersecurity
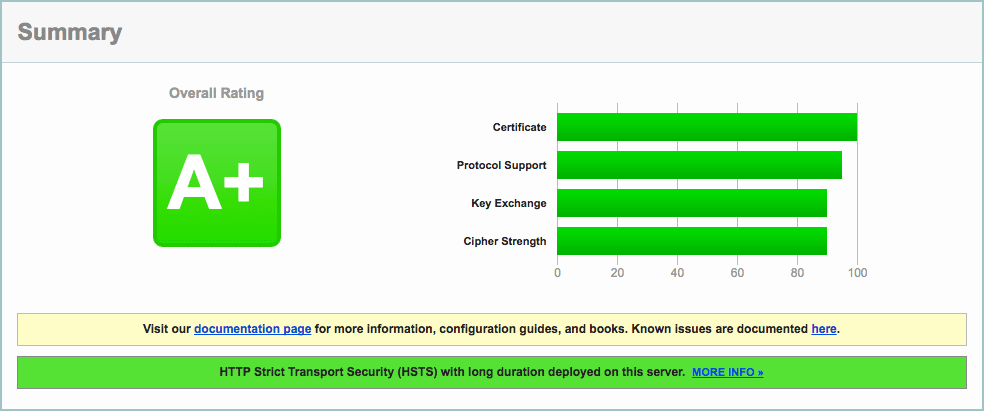
Organizations must ensure that they are utilizing solid, up-to-date cybersecurity methods. And for healthcare, that means HIPAA compliancy and HIPAA compliant email. Cybersecurity should include strong email filters, such as those offered with Paubox Email Suite Plus, to stop the onslaught of malicious emails. Both in-house and remote employees must be up-to-date with training and how to recognize a phishing email. Offline data backup and a data recovery plan are crucial if a phishing email attack unfortunately succeeds and ransomware is downloaded. Furthermore, sensitive or critical data (such as testing for COVID-19) must be stored separately from the main systems. While security agencies worldwide are working to identify and mitigate cyber issues, every organization must do their part to protect themselves using a layered cybersecurity program.
Subscribe to Paubox Weekly
Every Friday we'll bring you the most important news from Paubox. Our aim is to make you smarter, faster.