In 2020, cyber attacks against healthcare organizations doubled, as criminals capitalized on the instability and disruption caused by the COVID-19 pandemic. Even as communities today are working their way toward post-pandemic normalcy, the cybersecurity risks faced by the healthcare industry don't appear to be abating.
The latest high-profile victim of hackers surfaced on May 18, when the State of Alaska's Department of Health and Social Services (DHHS) confirmed that its official website was the target of a malware attack. The department had taken the website offline the night before as a precautionary measure.
“Unfortunately, this type of malicious attack is part of the cost of conducting any kind of business online as there are constant threats from people worldwide trying to infiltrate IT systems," Alaska health commissioner Adam Crum said in a press release. "I want to assure Alaskans that our department is doing everything possible to get our website back up and running safely and to understand the scope of the attack, its impacts, and how to prevent this from happening in the future.”
What is the Alaska DHSS?
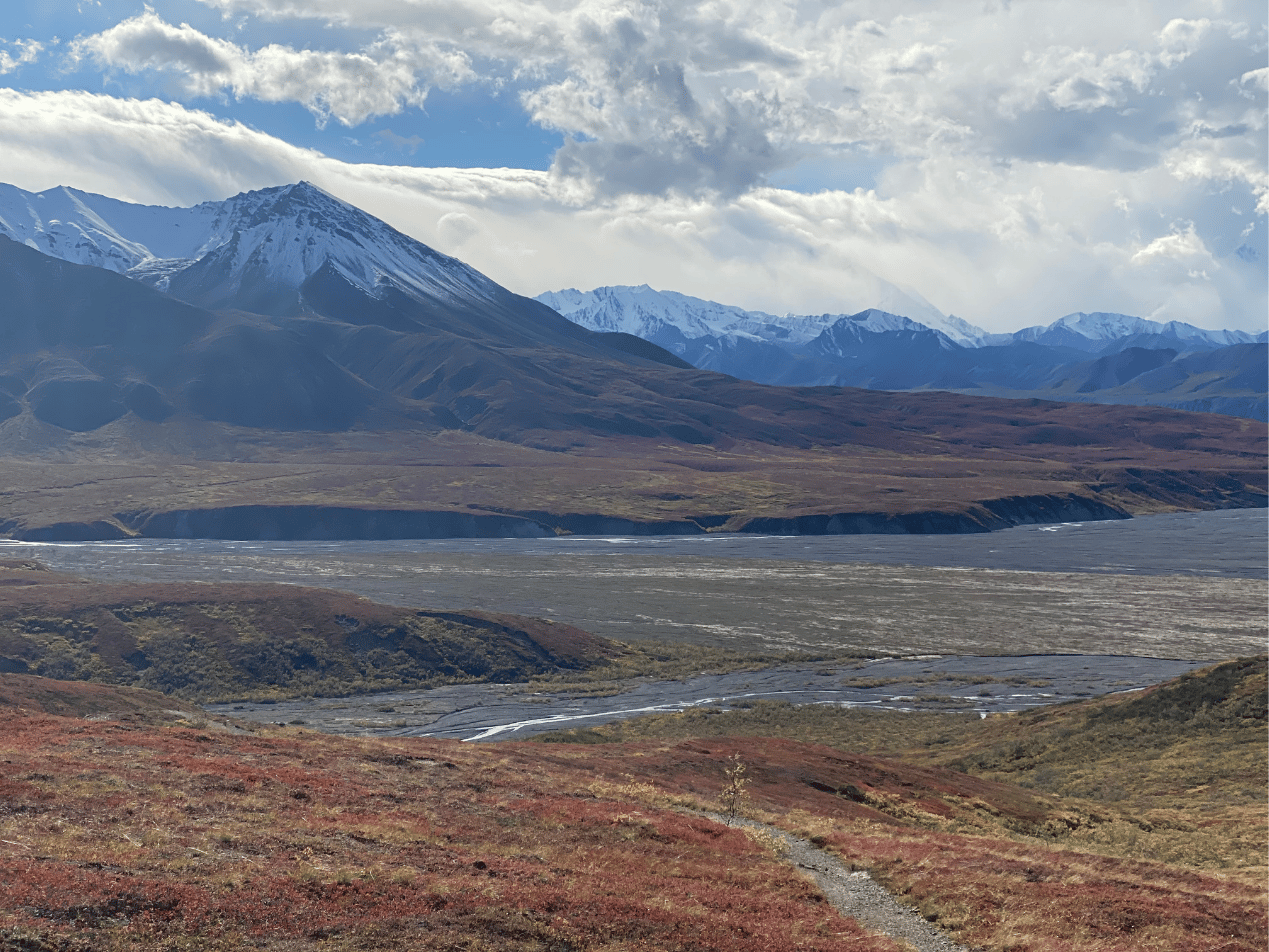
Based in Juneau, the DHSS oversees government healthcare initiatives that serve the 731,000 residents of the State of Alaska. Its mission is "to promote and protect the health and well-being of Alaskans." The department has a $3.4 billion budget, which was recently reduced in anticipation of lower demand for services as the COVID-19 pandemic subsides. Its website is a resource hub for many health services, including disseminating regular updates on COVID-19 case counts and vaccine availability.
What happened?
The DHSS is currently saying very little about the attack. "At this time, there are no details about who initiated the attack, why they targeted DHSS, whether this attack is related to any other recent attacks, or how long the website may be down," its announcement reads. "As is common with an investigation into this type of cyberattack, this one is expected to take some time to fully understand the full scope and impact of the incident." "Investigators are also in the process of determining whether any personal or confidential information was compromised," the statement continues.
The department did not respond when the media asked whether ransomware was involved. As a preventative measure, the DHSS website was taken down and replaced with a basic information page. As a result, Alaska residents cannot access a variety of resources and services, including the state's Behavioral Health and Substance Abuse Management System, its Vital Records System, the state's Temporary Assistance for Needy Families (TANF) program, and its childcare provider directory. DHHS says that it "is working as quickly as possible to ensure continuity of services to beneficiaries and providers," and notes that critical COVID-19 information—including vaccine appointment scheduling and data dashboards—can still be accessed.
SEE ALSO: The Costs of Ransomware Attacks
Has this happened before?
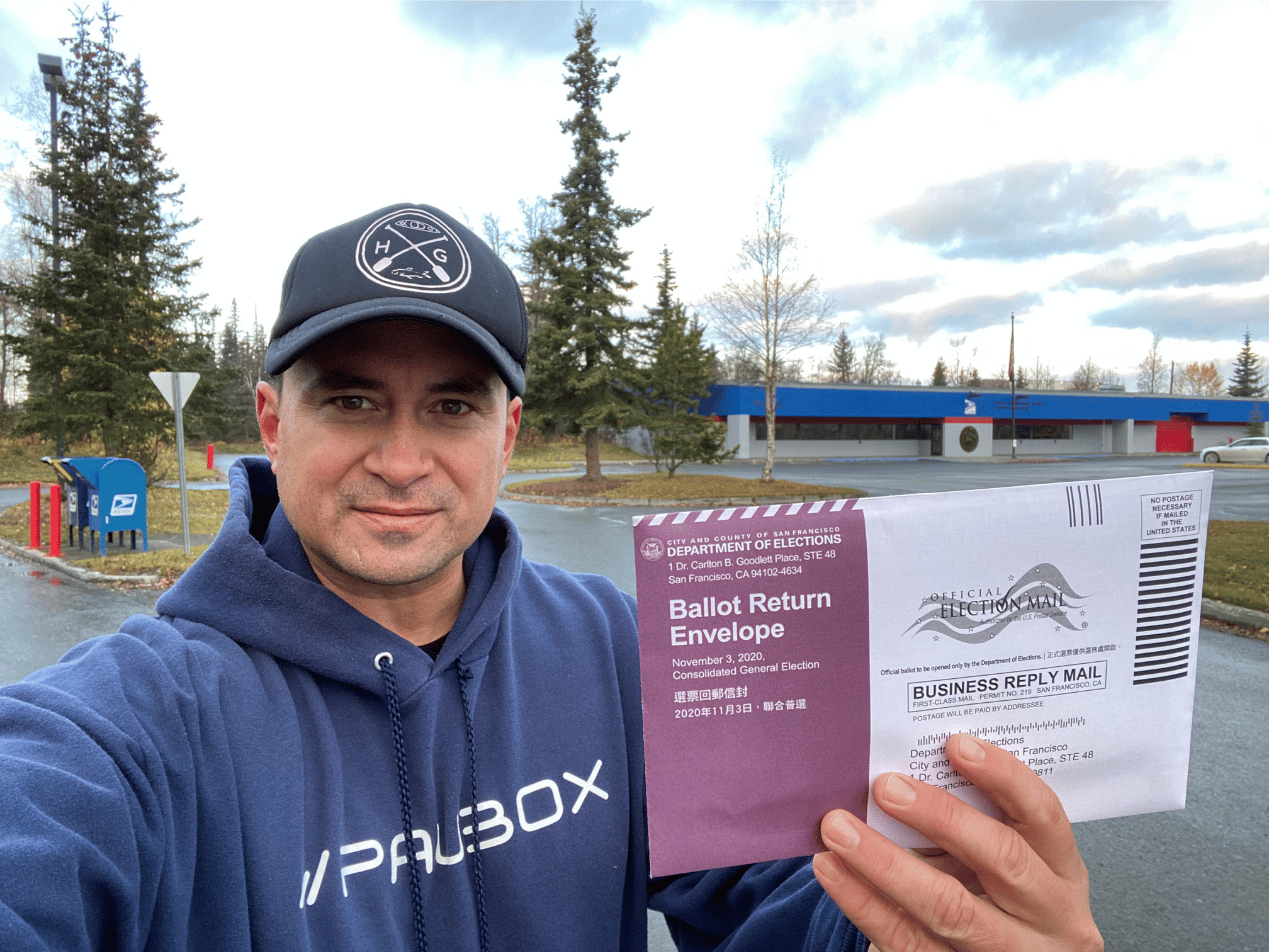
This incident is only the latest in a series of hacks targeting the Alaska state government. Less than a month ago, a malware attack on the Alaska court system brought its online services offline for several days. In October, Alaska's online voter registration system was compromised. In 2017 and 2018, the DHSS reported phishing attacks that affected over 700,000 individuals. And in 2012, DHSS was fined $1.7 million for violating HIPAA.
What happens next?
With almost no information on the nature of this latest attack, it's difficult to determine the ultimate outcome of the state's investigation. The most detail we could find on any of the recent attacks was that state employees noticed “anomalies in certain servers and personal computers.” No matter what the cause, protected health information (PHI) was accessed, so DHHS will need to issue a notice of the breach and will earn itself another mention on the federal Office of Civil Rights " Wall of Shame."
How to avoid becoming the next victim
Despite all the technical controls an organization might put in place, human error is the most common way that hackers gain access to internal systems. A reasonably convincing phishing email means one click is all it takes to breach your defenses. Investing in employee training is just as important as investing in cybersecurity services and tools. Paubox Email Suite Plus's inbound security features can keep those malicious emails from ever reaching an employee. Even better, it allows your employees to send HIPAA compliant email directly to a patient's inbox, without clumsy web portals or separate login credentials.
Subscribe to Paubox Weekly
Every Friday we'll bring you the most important news from Paubox. Our aim is to make you smarter, faster.